NFS搭建略..
创建nfs文件
安装部署1
2
3mkdir /opt/k8s-nfs-storage
echo "/opt/k8s-nfs-storage *(rw,no_root_squash,no_all_squash,sync)" > /etc/exports
exportfs -vr
所需要的yaml文件github:
修改deployment文件并部署deployment.yaml
需要修改的地方只有NFS服务器所在的IP地址(192.168.7.206),以及NFS服务器共享的路径(/opt/k8s-nfs-storage),两处都需要修改为你实际的NFS服务器和共享目录1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91kind: Deployment
apiVersion: extensions/v1beta1
metadata:
name: nfs-client-provisioner
spec:
replicas: 1
strategy:
type: Recreate
template:
metadata:
labels:
app: nfs-client-provisioner
spec:
serviceAccountName: nfs-client-provisioner
containers:
- name: nfs-client-provisioner
image: 192.168.19.111/gc/nfs-client-provisioner:latest
volumeMounts:
- name: nfs-client-root
mountPath: /persistentvolumes
env:
- name: PROVISIONER_NAME
value: idcsec.lan/nfs
- name: NFS_SERVER
value: 192.168.7.206
- name: NFS_PATH
value: /opt/k8s-nfs-storage
volumes:
- name: nfs-client-root
nfs:
server: 192.168.7.206
path: /opt/k8s-nfs-storage
---
kind: ServiceAccount
apiVersion: v1
metadata:
name: nfs-client-provisioner
---
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: nfs-client-provisioner-runner
rules:
- apiGroups: [""]
resources: ["persistentvolumes"]
verbs: ["get", "list", "watch", "create", "delete"]
- apiGroups: [""]
resources: ["persistentvolumeclaims"]
verbs: ["get", "list", "watch", "update"]
- apiGroups: ["storage.k8s.io"]
resources: ["storageclasses"]
verbs: ["get", "list", "watch"]
- apiGroups: [""]
resources: ["events"]
verbs: ["create", "update", "patch"]
---
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: run-nfs-client-provisioner
subjects:
- kind: ServiceAccount
name: nfs-client-provisioner
namespace: default
roleRef:
kind: ClusterRole
name: nfs-client-provisioner-runner
apiGroup: rbac.authorization.k8s.io
---
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: leader-locking-nfs-client-provisioner
rules:
- apiGroups: [""]
resources: ["endpoints"]
verbs: ["get", "list", "watch", "create", "update", "patch"]
---
kind: RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: leader-locking-nfs-client-provisioner
subjects:
- kind: ServiceAccount
name: nfs-client-provisioner
# replace with namespace where provisioner is deployed
namespace: default
roleRef:
kind: Role
name: leader-locking-nfs-client-provisioner
apiGroup: rbac.authorization.k8s.io
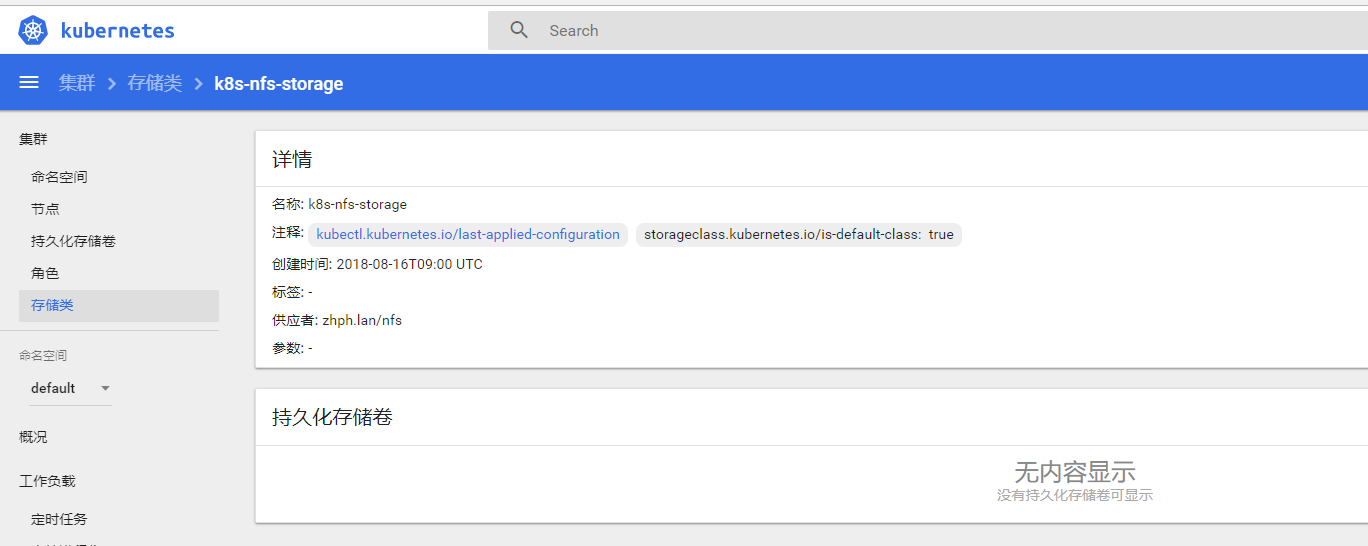
修改StorageClass文件并部署class.yaml
此处可以不修改,或者修改provisioner的名字,需要与上面的deployment的PROVISIONER_NAME名字一致。1
2
3
4
5apiVersion: storage.k8s.io/v1
kind: StorageClass
metadata:
name: k8s-nfs-storage
provisioner: idcsec.lan/nf
授权
RBAC授权文件在auth目录下面
如果您的集群启用了RBAC,必须授权provisioner。
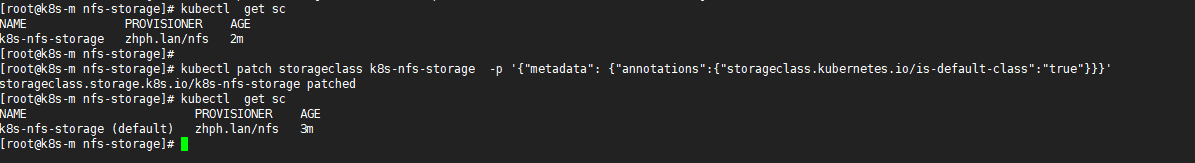
设置 k8s-nfs-storage作为默认存储类1
kubectl patch storageclass k8s-nfs-storage -p '{"metadata": {"annotations":{"storageclass.kubernetes.io/is-default-class":"true"}}}'
实例:1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17apiVersion: apps/v1beta1
kind: StatefulSet
metadata:
name: k8sapp
spec:
serviceName: "k8sapp"
replicas: 1
volumeClaimTemplates:
- metadata:
name: test
annotations:
volume.beta.kubernetes.io/storage-class: "k8s-nfs-storage"
spec:
accessModes: [ "ReadWriteOnce" ]
resources:
requests:
storage: 2Gi